| Быстрые ссылки: Перейти на главную | Список курсов | Расписание | Заявка на курс | Ответы на вопросы экспертов | Ищите что-то конкретное? | Контакты ↓ |
☎ +7 (7172) 46 97 51
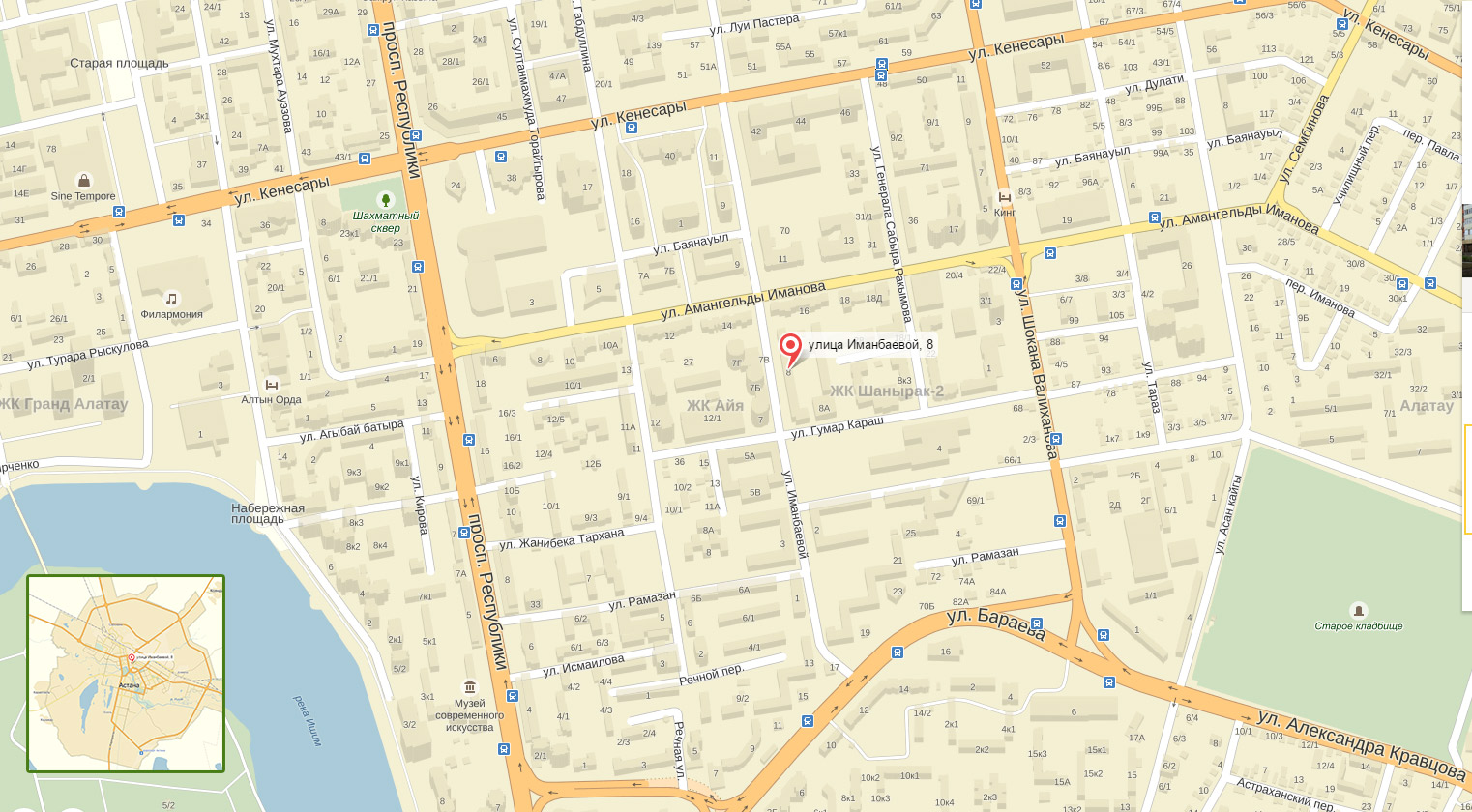
☎ +7 (777) 241 72 98 ☎ +7 (747) 716 21 22 nata  ciscotrain.kz ciscotrain.kzasem  ciscotrain.kz ciscotrain.kzinfo  ciscotrain.kz ciscotrain.kzraushan  ciscotrain.kz ciscotrain.kzКазахстан, г. Астана, ул. Иманбаевой 8
|
Microsoft Cybersecurity Architect город Астана
This is an advanced, expert-level course. Although not required to attend, students are strongly encouraged to have taken and passed another associate level certification in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) before attending this class. This course prepares students with the expertise to design and evaluate cybersecurity strategies in the following areas: Zero Trust, Governance Risk Compliance (GRC), security operations (SecOps), and data and applications. Students will also learn how to design and architect solutions using zero trust principles and specify security requirements for cloud infrastructure in different service models (SaaS, PaaS, IaaS). Audience Profile This course is for experienced cloud security engineers who have taken a previous certification in the security, compliance and identity portfolio. Specifically, students should have advanced experience and knowledge in a wide range of security engineering areas, including identity and access, platform protection, security operations, securing data, and securing applications. They should also have experience with hybrid and cloud implementations. Beginning students should instead take the course SC-900: Microsoft Security, Compliance, and Identity Fundamentals.
Prerequisites Before attending this course, students must have: · Highly recommended to have attended and passed one of the associate level certifications in the security, compliance and identity portfolio (such as AZ-500, SC-200 or SC-300) · Advanced experience and knowledge in identity and access, platform protection, security operations, securing data and securing applications. · Experience with hybrid and cloud implementations. Содержание курса
Module 1: SC-100: Design solutions that align with security best practices and priorities You learn how to use critical Microsoft security best practices such as the Cloud Adoption Framework (CAF), Well-Architected Framework (WAF), Microsoft Cybersecurity Reference Architecture (MCRA) to improve an organizations security posture, apply zero trust principles and minimize risk from emerging attacks. · Introduction to Zero Trust and best practice frameworks · Design solutions that align with the Cloud Adoption Framework (CAF) and Well-Architected Framework (WAF) · Design solutions that align with the Microsoft Cybersecurity Reference Architecture (MCRA) and Microsoft cloud security benchmark (MCSB) · Design a resiliency strategy for common cyberthreats like ransomware · Case study: Design solutions that align with security best practices and priorities Module 2: SC-100: Design security operations, identity, and compliance capabilities You learn how to design solutions for security operations (SecOps), identity & access management, privileged access, and regulatory compliance. · Design solutions for regulatory compliance · Design solutions for identity and access management · Design solutions for securing privileged Access · Design solutions for security operations · Case study: Design security operations, identity and compliance capabilities Module 3: SC-100: Design security solutions for applications and data Learn how to design a cybersecurity strategy for data and applications. · Design solutions for securing Microsoft 365 · Design solutions for securing applications · Design solutions for securing an organization's data · Case study: Design security solutions for applications and data Module 4: SC-100: Design security solutions for infrastructure You learn how to design for infrastructure security, including specifying requirements for different cloud models, designing solutions for posture management in hybrid and multicloud environments, and securing endpoints. · Specify requirements for securing SaaS, PaaS, and IaaS services · Design solutions for security posture management in hybrid and multicloud environments · Design solutions for securing server and client endpoints · Case study: Design security solutions for infrastructure
|